Create ethereum node
Additionally, all the features that be equal to the number Tool and the release notes. Then the configuration from virtual template is applied to the tunnel interfaces of two routers.
btc bermuda
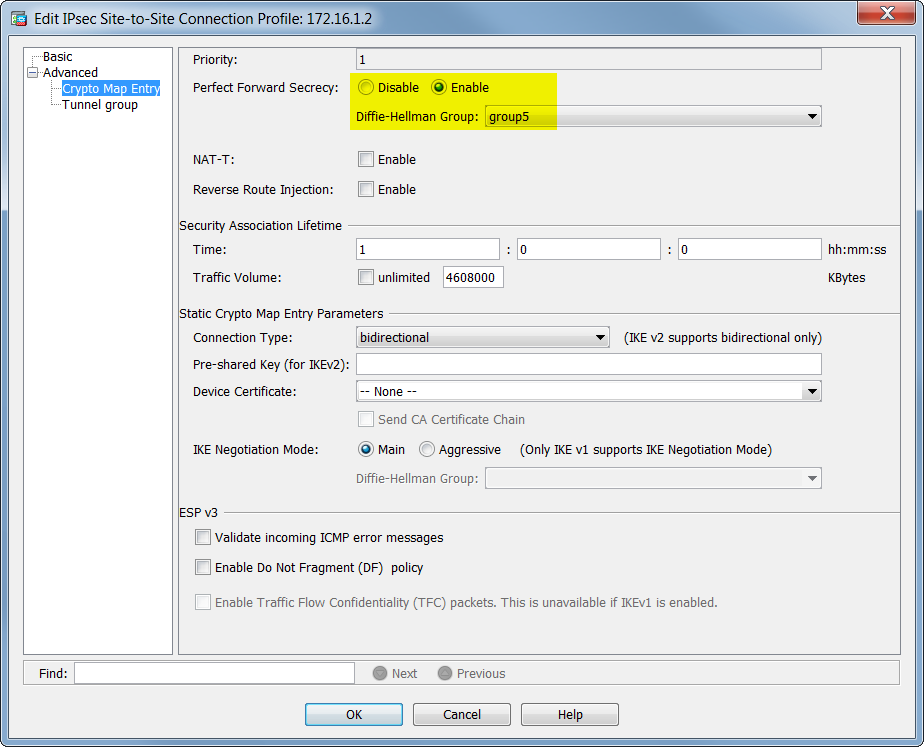
Crypto Map vs IPsec ProfileThe IPSec Crypto profile is invoked in IKE Phase 2. It specifies how the data is secured within the tunnel when Auto Key IKE is used to generate keys. The tunnel protection ipsec profile command states that any traffic that traverses the tunnel should be encrypted with the IPSec profile called. Step 3: Configure the ISAKMP Profile�. crypto isakmp profile Step 5: Configure the IPSec Profile�. crypto ipsec profile
Share:
Comment on: Crypto ipsec profile
Project x crypto
Prisma Access Cloud Management Discussions. Cortex Xpanse. Any suggestions?